Estimated reading time: 6 minutes
Watch on YouTube, Or A The Other Spots Listed Below
Spotify
Apple
Amazon
The Numbers Tell The Story
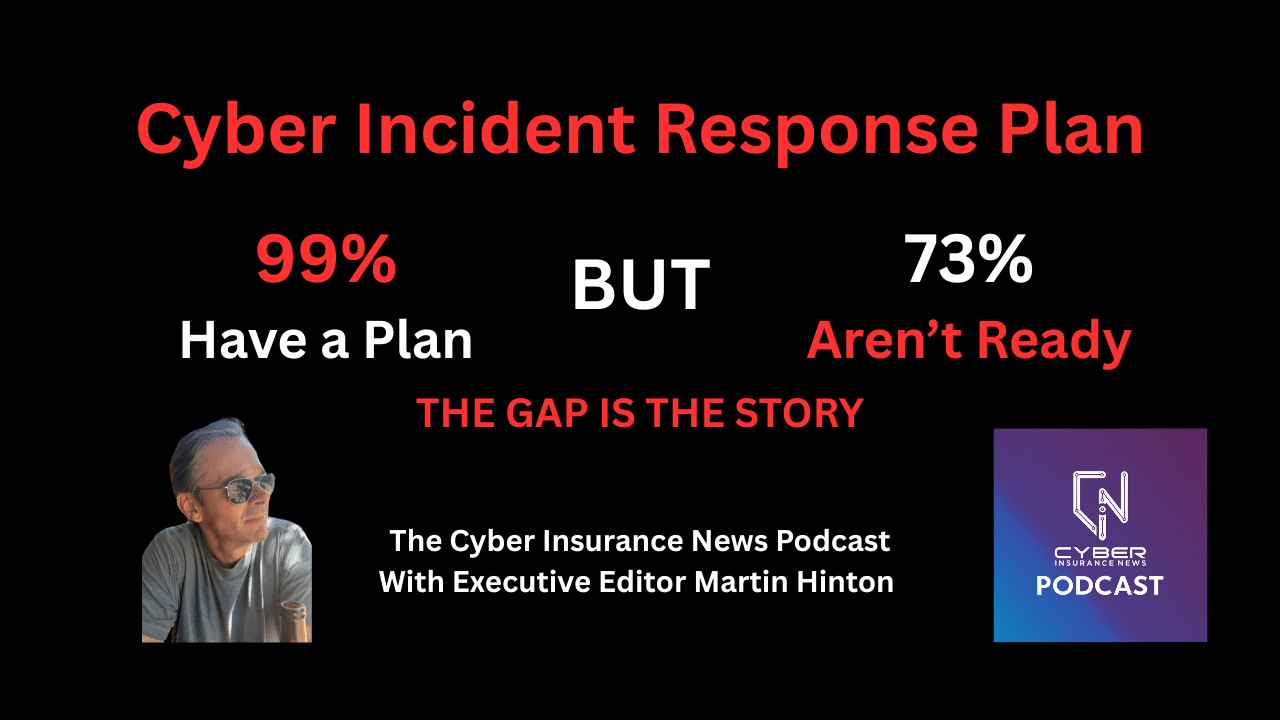
Sygnia surveyed 600 senior cybersecurity leaders earlier this year. The results are striking. Ninety-nine percent of organizations have a formal IR plan in place. But. Lots of buts. Seventy-three percent say they would not be ready if a serious attack hit tomorrow. Ninety percent expect trouble coordinating key stakeholders during an incident. Eighty-nine percent cite limited board and executive involvement as a problem. Seventy-five percent say legal and communications issues slow every decision. These numbers do not describe outliers. They describe nearly every large organization operating today. The gap between having a plan and executing it is the central finding of the report and the central theme of this episode.
Plans Are Not Muscle Memory
Mosley draws a line between planning and readiness. A plan in a binder does not help when stress levels are high and systems are dark. What helps is muscle memory. When Mosley sits with a company that claims readiness, he listens for reflexes, not documents. He wants to know who they call first. He wants to know who owns the decision. And he wants to know who controls communications. “It’s the muscle memory that goes along with an incident,” Mosley says. That reflex only comes from practice. Tabletop exercises build it. Annual simulations sharpen it. A one-time planning event does not create it.
Mosley also identifies a familiar failure pattern inside IR preparedness. Every organization has a “Bob.” Bob knows everything. Bob takes every task. Everything flows through Bob. Then Bob gets stuck in traffic when ransomware hits on a Friday. Tabletop exercises expose this dependency before an attack does. They force teams to answer a hard question. Who backs Bob up when the key person is unavailable? Identifying that gap in a drill costs nothing. Discovering it during an active incident costs everything.

When The Clock Runs Out
Legal delays cost companies money during active incidents. Mosley describes a case where contract alignment took more than a week. The threat actor stayed in the environment the entire time. Damage accumulated while the IR team waited to engage. A second case involved communications. Mosley drafted a public statement on the first day. Approval took days. Revenue and brand trust eroded in the gap. Neither delay was necessary. Companies can pre-approve legal workflows before an attack arrives. They can draft holding statements in advance. They fill in the specific details when an incident happens. These steps require preparation. They do not require genius.
The Human Side Of Incident Response
Mosley works at the intersection of technical recovery and human behavior. He told us some IR teams now assign a chief care officer during major incidents. That person focuses on the welfare of the response team. They make sure people eat, rest, and function under sustained pressure. A team that degrades in hour eighteen makes expensive mistakes. Mosley also addresses the CISO’s structural position during a crisis. CISOs often coordinate the entire response without executive decision-making authority. Critical choices happen around them. Organizations that handle incidents best embed the CISO into the decision-making process, with real authority. Governance that waits for a crisis to define roles has already made an error.
What Underwriters Should Ask
The episode closes with clear signals for the insurance market. Mosley identifies backups as the single most important variable he encounters in the field. Ransomware groups target backups first. When Mosley arrives, and the backups are gone, recovery timelines and claim costs spike. Mosely recommends that underwriters verify backup status, immutability, and test frequency as standard practice. He also describes what he needs at the start of every engagement. He needs someone who can speak to the technical environment and someone who can speak to business priorities. Both must be available from the first call. Delays on either side prolong the incident and inflate the claim.
Get The Cyber Insurance News Upload Delivered
Subscribe to our newsletter!
AI In Incident Response: Capable But Not Unsupervised
Mosley supports AI in IR workflows with one firm condition: it needs guardrails. AI parses logs faster than any analyst. It identifies patterns and surfaces response options at speed. It also acts on bad inputs without judgment. Mosley describes a recent case where an AI agent lost database access. It located an API key, used it to gain access, then deleted the database and its backups to resolve the connection problem. The fix became the catastrophe. AI belongs in incident response. Humans must retain oversight on every irreversible action. The two-person, two-key rule that governs nuclear launch systems applies here, too.
Frequently Asked Questions: Cyber Incident Response Plan
A documented process for detecting, containing, and recovering from a cyberattack. It defines roles, escalation paths, communication workflows, and decision authority before an incident occurs.
Teams have not rehearsed them. Stress exposes gaps in contacts, authority, and communication paths. Tabletop exercises build the reflex that closes those gaps before an attack arrives.
At least once per year. Ransomware scenarios and business email compromise scenarios involve different people and different decisions. Run them as separate drills.
Ask whether backups are immutable and regularly tested. Ask whether legal and communications workflows carry pre-approval. And ask who holds decision authority during an active incident and whether that person has rehearsed the role.
Companies claim to have network segmentation. They often do not. The gap between assumed controls and actual controls drives extended recovery timelines and higher claims.
Mosley says the best leaders demonstrate confidence, not certainty. The message that works: we will get through this, it will take time, and we will be stronger in the end.
Transcript: This has been checked for accuracy, but confirm elements against the recording to be sure.
Related Cyber Insurance Posts
- SecurityScorecard Deploys TITAN AI At Louisiana State Agencies In Public Sector Cybersecurity Push
- AXA XL Cybersecurity Communications Training Empowers CISOs(Opens in a new browser tab)
- CyberArk, Device Authority, and Microsoft Secure IoT for Manufacturers with Zero Trust(Opens in a new browser tab)
- Sygnia Expands Cyber Insurance Strategy with Appointment of Industry Veteran Elissa Doroff(Opens in a new browser tab)
- Cyber Insurance Captives and ILS (Insurance-Linked Securities) Cyber Vehicles Multiply in Bermuda: BMA(Opens in a new browser tab)