Estimated reading time: 10 minutes
A new global survey of 600 senior cybersecurity leaders reveals a troubling gap. Nearly every organization has a formal incident response plan. But almost three-quarters of the people responsible for those plans say they would not work under real pressure. That disconnect sits at the heart of the 2026 CISO Survey: The State of Incident Response Readiness, published today by Sygnia, the global cyber readiness and response firm.
The survey was conducted by Vanson Bourne in January and February 2026. It covers organizations with more than 1,000 employees and over $250 million in annual revenue across the United States, Canada, Mexico, the UK, France, Germany, the Benelux, Australia, and Singapore. Key sectors include retail, financial services, manufacturing, private healthcare, and crypto and decentralized finance.
Plans Exist. Confidence Does Not
The most striking finding in the report is not how few organizations have incident response plans. It is how little those plans are trusted. Ninety-nine percent of respondents have a formal IR plan in place. But only 32% to 39% rate any single element of their IR capability as highly effective. Those elements include 24/7 monitoring, digital forensics, defined roles and escalation paths, and tabletop testing.
Having a plan on paper is not the same as being able to execute it under pressure. The report makes this clear. Fewer than one in three respondents rate their tabletop testing as highly effective. Digital forensics capability rates are even lower. These are the tools organizations reach for first when an attack hits.
The practical gap between planning and performance is the central issue. 73% of senior cybersecurity decision-makers say their organization would not be fully ready if a serious attack occurred tomorrow. That figure holds despite near-universal adoption of formal plans and tools.
Coordination Breakdown Is The Real Problem
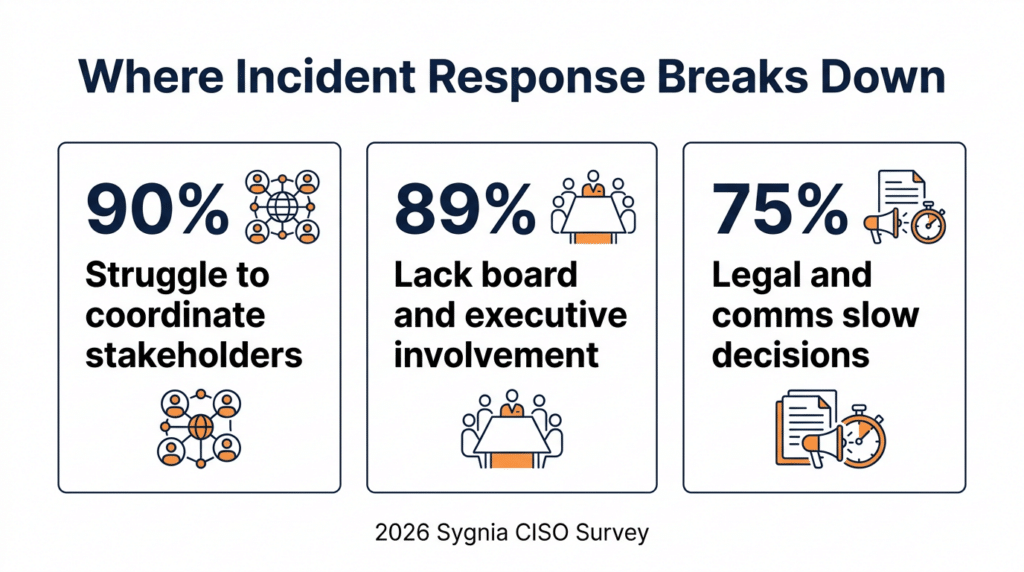
The report identifies three reasons for this gap. The first and most significant is organizational friction. When an attack happens, the people who need to make quick decisions cannot align quickly enough.
Ninety percent of respondents say they would struggle to coordinate key stakeholders during a significant incident. Eighty-nine percent say limited board and executive involvement in IR readiness is a challenge. Seventy-five percent say uncertainty about when and how to involve legal and communications teams slows decision-making.
This is not a technology problem. It is a leadership and governance problem. When authority is unclear and executives are not rehearsed, technical progress stalls while people wait for approvals. The attack keeps moving. The response does not.
This finding lines up directly with work done on this site. In a recent Cyber Insurance News podcast, Max Martina, president of Cambridge Leadership Associates, made a sharp distinction between technical problems and adaptive ones. Cyber risk, he argued, is an adaptive challenge. It requires organizations to change how they think and act, not just deploy better tools. The Sygnia data puts hard numbers on that argument. Plans and tools are in place almost everywhere. What is missing is the cross-functional alignment and executive engagement to make them work.
Board Absence Makes It Worse
The board and executive engagement finding deserves its own attention. Eighty-nine percent of respondents cite limited board or executive involvement in IR readiness and decision-making as a challenge. This is not a gap in technology investment. It is a gap in governance.
When executives are not part of IR rehearsals before a crisis, they get briefed during one. Teams spend time re-explaining the situation instead of acting on it. Decisions slow down. Containment slows down. Costs go up.
The report recommends that organizations run executive tabletop exercises and establish structured IR retainers with defined escalation authority before an attack happens, not after. The goal is to ensure leadership is embedded in the response process, not introduced mid-crisis.
Blind Spots Across Cloud And OT
The second major theme is visibility. 78% of respondents say blind spots in their environment risk persistent attacker access and increase the likelihood of repeat incidents. They cannot fully see what is happening across their own systems.
Public cloud tops the list of blind spot concerns at 90%. On-premises infrastructure, endpoints, OT and ICS environments, and SaaS platforms all follow at 89%. These are not obscure corners of the IT estate. They are the core environments where modern business runs.
The OT finding carries particular weight. Eighty-four percent of respondents are concerned about attackers crossing from corporate IT systems into operational technology and industrial control system environments. When an attack reaches OT, the consequences change. Operational shutdowns become more likely. Recovery takes longer. The financial and reputational damage compounds.
The report is clear that closing visibility gaps requires more than better tools. It requires unified investigative capability across all environments, combined with regular testing to confirm that visibility actually translates into the ability to contain threats.
Get The Cyber Insurance Upload Delivered
Subscribe to our newsletter!
Attacks Are Common. The Damage Is Real
The frequency data in the report removes any sense that these are theoretical risks. 76% of organizations in the survey experienced at least one cyberattack in the past 12 months. Almost a third experienced more than one.
The impact of those attacks was significant. Forty-seven percent experienced an operational shutdown. Forty-one percent reported data loss. Forty-one percent suffered reputational damage. Forty percent lost revenue. These are not near misses. They are material business events with financial consequences.
Retail is the sector most likely to report not being fully ready, followed closely by crypto and decentralized finance. North America reports the highest attack frequency. APAC reports the worst outcomes in terms of data loss and reputational damage. Private healthcare faces the highest legal and communications friction during incidents, with 86% of respondents in that sector reporting that legal and communications delays slow their response.
AI Is Growing, But Cannot Replace Judgment
The third theme is AI in incident response. Today, about a third of organizations report extensive AI use across threat detection and IR activities. That is up from 25% last year. By 2027, 63% expect AI to be embedded across their detection and response operations.
The data shows that AI does help when it is properly built into IR workflows. Organizations with moderate or extensive AI use are consistently more likely to rate their IR components as effective than those with limited AI use. The gap is meaningful across every component, from documented plans to digital forensics.
But the report is direct on the limits. AI adoption is outpacing the consideration of its security implications. Rapid adoption introduces AI as a new attack surface. Threat actors can exploit it through techniques including LLM poisoning and deepfakes. Strong AI risk management requires governance, regulatory compliance, ongoing oversight, and lifecycle management. AI should accelerate IR capability, not substitute for it.
Two-thirds Plan To Switch IR Providers
One of the more revealing findings involves IR provider satisfaction. Sixty-five percent of respondents say they are likely to switch their incident response provider at the end of their current contract. The main drivers are the need for more proactive readiness support, broader coverage across IT, OT, and cloud environments, and deeper expertise in complex incidents.
Seventy-nine percent agree that relying on IR providers that are not vendor-agnostic could leave critical risks unaddressed. When a provider is tied to a single tooling ecosystem, their visibility and recommendations are bound by what their tools can see. That boundary can be the gap an attacker moves through.
What This Means For Cyber Insurance
The Sygnia report is directly relevant to how underwriters and brokers assess cyber risk. The most important implication is one the data makes hard to ignore: having an IR plan is not, on its own, a meaningful risk signal. Almost every large organization has one. The question is whether that plan has been tested with executive participation, integrated with legal and communications functions, and validated across the full environment, including cloud and OT.
Organizations where boards are not rehearsed, where legal and comms are uncertain about their roles during an incident, and where visibility gaps persist across cloud and OT environments face longer containment times, larger business interruption losses, and higher reputational costs when attacks occur. The 47% operational shutdown rate and the 40% lost revenue rate in this survey are the financial story behind those governance gaps.
For underwriters pricing business interruption coverage, the question of how quickly an insured can authorize containment is a direct driver of expected loss. The Sygnia data provides a new empirical foundation for those questions.
FAQ Incident Response Readiness
Q: What did the Sygnia CISO survey find about incident response readiness?
A: The 2026 Sygnia CISO Survey found that 73% of senior cybersecurity leaders say their organisation would not be fully ready if a serious cyberattack happened tomorrow. This is despite 99% having a formal IR plan. Fewer than 40% rate any element of their IR capability as highly effective. The gap between having a plan and being able to execute it is the core finding.
Q: Why does having an IR plan not mean an organisation is prepared?
A: Plans require coordinated execution to work. The survey finds 90% of organisations would struggle to coordinate key stakeholders during an attack. Eighty-nine percent cite limited board and executive involvement as a challenge. Seventy-five percent say legal and communications uncertainty slows decisions. Without cross-functional alignment and executive engagement, even a strong plan stalls under pressure.
Q: How common are cyberattacks among the organisations surveyed?
A: Seventy-six percent of organisations in the survey experienced at least one cyberattack in the last 12 months. Almost a third experienced more than one. Forty-seven percent reported an operational shutdown as a result. Forty-one percent reported data loss. Forty percent reported lost revenue. These are recurring business events, not rare incidents.
Q: What role should the board play in incident response readiness?
A: The report says IR must be owned at both the security and executive levels, with defined decision rights and pre-agreed escalation pathways. Boards should take part in regular tabletop exercises before a crisis happens, not learn the IR process during one. When executives are introduced mid-incident, teams spend time briefing instead of acting. That delay directly increases loss severity.
Q: What are the biggest visibility gaps organisations face during an incident?
A: Public cloud is the top blind spot, cited by 90% of respondents. On-premises infrastructure, endpoints, OT and ICS environments, and SaaS platforms follow closely at 89% each. Eighty-four percent are concerned about attackers crossing from corporate IT into operational technology environments. Without visibility across these areas, teams cannot confirm where an attack has moved or what it has affected.
Q: Why is the OT and ICS finding important for cyber insurers?
A: When attacks reach operational technology environments, the consequences escalate sharply. Operational shutdowns become more likely. Recovery takes longer. Business interruption costs grow. Eighty-four percent of respondents are concerned about this crossing point. For underwriters pricing BI coverage in manufacturing, energy, and healthcare, OT visibility and segregation are direct drivers of expected loss severity.
Q: Does AI improve incident response readiness?
A: It helps when built into workflows properly. Organisations with moderate or extensive AI use consistently rate their IR components as more effective than those using AI in a limited way. But the report warns that AI adoption is outpacing security governance. AI introduces new attack surfaces including LLM poisoning and deepfakes. It should accelerate IR capability, not replace the human judgment and executive alignment that effective response requires.
Q: What does the IR provider switching data tell us?
A: Sixty-five percent of respondents plan to switch IR providers at contract end. The main reasons are insufficient proactive readiness support, limited coverage across IT, OT, and cloud, and a lack of expertise in complex incidents. Seventy-nine percent also worry that non-vendor-agnostic providers leave critical risks unaddressed. For insurers that rely on panel IR providers, this data raises questions about the quality and breadth of those retainers.
Q: Which sectors face the greatest IR readiness challenges?
A: Retail and crypto and decentralised finance report the lowest IR readiness. Private healthcare faces the highest legal and communications friction, with 86% saying those functions slow decisions during incidents. Retail is most exposed to operational shutdowns and revenue loss. Manufacturing and financial services skew toward data loss. Each sector profile carries different implications for underwriters pricing sector-specific cyber coverage.
Q: How should underwriters use this data when assessing cyber risk?
A: The report suggests that asking whether an insured has an IR plan is the wrong question. Almost every large organisation does. The better questions are whether the plan has been tested with executive participation, whether legal and communications roles are defined in advance, and whether visibility covers cloud, endpoints, and OT environments. Organisations that cannot answer yes to those questions face longer containment times and higher BI losses when attacks occur.
Related Cyber Liability Insurance Posts
- Two-Thirds Of Cybersecurity Staff Consider Leaving Their Employer
- Protect Your Brand, Not Just Your Data: The Critical Role of ERM in Cyber Risk
- Rich Boomers Lag on Personal Cyber Insurance: Report
- The Looming Global Cyber Crisis: Are We On The Doorstep of Digital Disaster?
- The Uncomfortable Truth About Cybersecurity: Why Awareness Month Is Not Enough
