Estimated reading time: 8 minutes
A critical flaw in Adobe Reader was actively exploited for at least five months before Adobe issued a fix. Attackers stole files from victims’ computers during that entire period. The trigger required was simple: opening a PDF. This episode exposes a structural problem in how patch management works and directly challenges one of the most common controls underwriters rely on at renewal.
A Five-Month Window Attackers Used Before Any Patch Existed
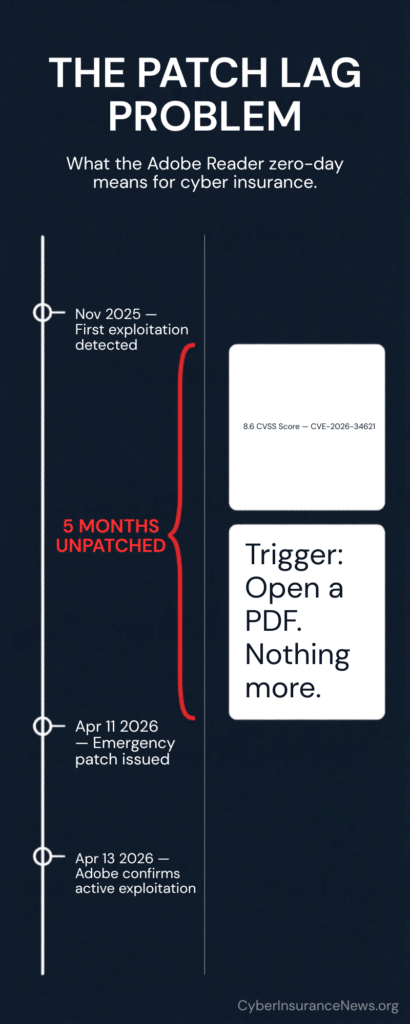
Adobe issued emergency bulletin APSB26-43 on April 11, 2026, confirming that CVE-2026-34621 was actively exploited in the wild. Adobe rated it Priority 1, its highest urgency classification. Security researcher Haifei Li of EXPMON found malicious samples dating the exploitation back to at least November 2025. Adobe stated it is “aware of CVE-2026-34621 being exploited in the wild.” That is five months between the first known exploitation and vendor acknowledgment.
This matters directly for underwriting. Cyber insurance applications can ask whether insureds patch critical vulnerabilities within 30 or 72 hours of vendor disclosure. CVE-2026-34621 shows that disclosure date and exploitation start date are not the same thing. Enterprises that rely on vendor bulletins to drive their patch cycles had no bulletin to act on for five months. Patch compliance measured from disclosure dates does not capture this gap.
Opening A File Is The Entire Attack
CVE-2026-34621 sits in the JavaScript layer Adobe Reader uses to process PDF files. A malicious PDF exploits it the moment it opens. No macro needs enabling. No additional click occurs. The attack executes automatically inside Reader. When researchers submitted the first malicious sample to VirusTotal, only 13 of 64 antivirus engines flagged it. Traditional endpoint tools missed it. Users had no warning and made no error.
This directly undermines the defense underwriters most commonly see on cyber applications: security awareness training. Training cannot stop a threat that requires no user mistake. An employee, following the normal process of opening a PDF, triggered the exploit. That shifts the underwriting conversation from behavior to architecture: specifically, whether application-layer software receives the same patch priority as operating systems and firewalls.
File Theft Without Ransomware Triggers Claims Earlier Than Expected
Researchers confirmed two capabilities from samples found in the wild. The exploit pulls JavaScript from a remote server and executes it inside Reader. It also steals arbitrary local files and transmits them externally. File exfiltration alone is enough to trigger a data breach claim under most cyber policies. Ransomware deployment is not required. An organization whose files were silently removed between November 2025 and April 2026 may not yet know it has a claim. The attacker collected data and left. No encryption. No ransom note. And no visible disruption.
Get The Cyber Insurance News Upload Delivered
Subscribe to our newsletter!
What This Means For Patch Management At Renewal
Three questions apply immediately. First: Does the insured’s patch program cover application-layer software like Adobe Reader, not just operating systems and network infrastructure? Many patch frameworks miss widely deployed endpoint applications entirely. Second: Does the insured have endpoint detection that can identify unusual file access or outbound data transfers initiated by a PDF application? The exploit used legitimate Adobe APIs as its channel perimeter tools are unlikely to flag legitimate application behavior. Third: has the insured audited outbound data transfer activity from Adobe Reader processes since November 2025? If not, a claim may already exist that has not been identified.
Brokers should also flag this to clients running Acrobat DC or Acrobat Reader DC version 26.001.21367 or earlier, and Acrobat 2024 version 24.001.30356 or earlier, on Windows and macOS. The patched versions are 26.001.21411 for DC and 24.001.30362 for Acrobat 2024 on Windows. If patching is not immediately possible, Adobe recommends blocking all outbound HTTP traffic that contains the “Adobe Synchronizer” string in the User-Agent field as an interim measure.
CVE-2026-34621 exemplifies modern threats: exploited quietly in widely used software, often before any warning is issued.
Frequently Asked Questions
What CFOs and General Counsel need to know about patch management, CVE-2026-34621, and cyber insurance
CVE-2026-34621 is a critical flaw in Adobe Acrobat and Adobe Reader that allows an attacker to steal files or execute malicious code when a user simply opens a PDF. No additional clicks or actions are needed. Adobe confirmed it was actively exploited in the wild and issued an emergency patch on April 11, 2026. The flaw was being exploited from at least November 2025 — five months before the patch arrived.
Almost certainly yes, if data was accessed or exfiltrated. File theft through a technical exploit meets the breach trigger in most cyber policies. However, if the malicious PDF arrived via invoice-themed phishing, coverage may also extend to your social engineering or funds transfer fraud section. Review your policy’s breach definition and loss trigger language carefully. Coverage disputes at claim time often hinge on which section applies.
Not necessarily for this vulnerability. CVE-2026-34621 was exploited for five months before Adobe issued any public bulletin. A 30-day patch policy measured from vendor disclosure would have provided no protection during that window. Underwriters are beginning to recognise this gap. Patch compliance measured from disclosure dates does not capture vulnerabilities that are actively exploited before public acknowledgment. Review how your policy defines patch obligations.
Yes. The exploit can silently exfiltrate local files without triggering a full ransomware deployment. If your endpoints ran vulnerable Adobe Reader versions between November 2025 and April 2026, and a user opened a malicious PDF during that period, data may have been stolen without any visible disruption. Instruct your IT or security team to audit outbound data transfers and Adobe Reader activity logs from that period. Notify your insurer promptly if suspicious activity is found.
Three immediate steps. First, confirm your IT team has deployed Adobe’s emergency patch to all endpoints running Acrobat or Acrobat Reader — the fixed version is 26.001.21411 for DC and 24.001.30362 for Acrobat 2024. Second, brief staff not to open PDF attachments from unknown senders until patching is confirmed. Third, ask your security team to review outbound network activity from Adobe Reader processes over the past six months. Report any anomalies to legal and your insurer before taking remediation steps that could affect forensic evidence.
Increasingly, yes. Underwriters are expanding patch management questions beyond operating systems and firewalls to cover widely deployed applications. Adobe Reader is installed on virtually every enterprise endpoint. Its patch status is a measurable, verifiable control. Expect renewal applications to include questions about application-layer patching cadence, not just infrastructure patching. Demonstrate you have a process that covers endpoint applications, not just servers.
Not against the technical exploit itself. CVE-2026-34621 triggers when a PDF is opened — a routine, expected action. No employee made an error. The attack used invoice-themed lures, which means a trained employee following normal process could still trigger it. Training remains valuable for reducing phishing click rates broadly, but it cannot substitute for patching application-layer software. Underwriters are recognising this and shifting weight toward technical controls over training attestations.
CVE-2026-34621 illustrates the trend that leading cyber reports have identified: attackers are moving faster than disclosure and patching cycles can respond. CrowdStrike’s 2026 Global Threat Report found average breakout times fell to 29 minutes. CyberCube’s April 2026 briefing concluded that recovery capability now determines business interruption severity more than detection speed. Silent exploitation of widely deployed software is the mechanism behind both findings. Patch lag is no longer a hygiene issue. It is a pricing variable.
Patch lag is the time between a vulnerability being known and an organisation deploying the fix. Insurers care because it directly predicts how quickly an attacker can convert initial access into a loss. The longer the lag, the wider the window for data theft, ransomware, or operational disruption. CVE-2026-34621 adds a new dimension: lag measured from exploitation start, not disclosure date. Insurers are beginning to ask about continuous vulnerability monitoring, not just patch compliance against bulletin dates.
Consult your legal counsel and broker before deciding, but the general principle is this: if you have reason to believe a breach may have occurred — including running vulnerable software during an active exploitation period — many policies require notification of a potential claim, not just a confirmed one. Late notification is one of the most common grounds for coverage disputes. Do not wait for confirmation of data loss before raising the issue with your broker and legal team.
Related Cyber Liability Insurance Posts
- AI Is Rewriting Cyber Insurance Requirements
- Protect Your Brand, Not Just Your Data: The Critical Role of ERM in Cyber Risk
- What a Difference a Day Makes: Berkley Sues as a Cyber Insurance Subrogee to Recover Claim Settlement
- UK Cyber Report Calls for Growth, Stronger Cyber Insurance, and Clearer Rules
