Estimated reading time: 7 minutes
Resilience’s 2025 cyber insurance claims data shows that ransomware groups are now focusing on stealing data to gain leverage. Data-suppression extortion rose from 49% in the first half of the year to 65% in the second half. In 57% of attacks, criminals used data theft to get around stronger backups. Infostealers collected over two billion credentials and often signaled a breach before ransomware attacks. Interlock looked for stolen files in cyber insurance policies and changed their demands based on coverage limits. Vendor failures caused 18% of losses as attackers took advantage of password resets and compromised open-source repositories. This shift shapes the rest of the report, which explains how these tactics are changing loss drivers, response costs, and coverage choices.
“Cyber risk is constantly changing. As cybercriminals shift their tactics, a new reality is setting in: the real risk is about more than a security incident’s immediate disruption, it’s about the long-tail aftershocks that follow,” said Vishaal “V8” Hariprasad, Co-Founder and CEO of Resilience.

Extortion Moves From Encryption To Data Exposure
Resilience reports that attackers now seek longer-lasting leverage. The report describes a shift from using encryption to disrupt operations to using data theft for reputational pressure. The data backs this up: attacks involving only data theft made up 49% of extortion claims in the first half of the year and increased to 65% in the second half.
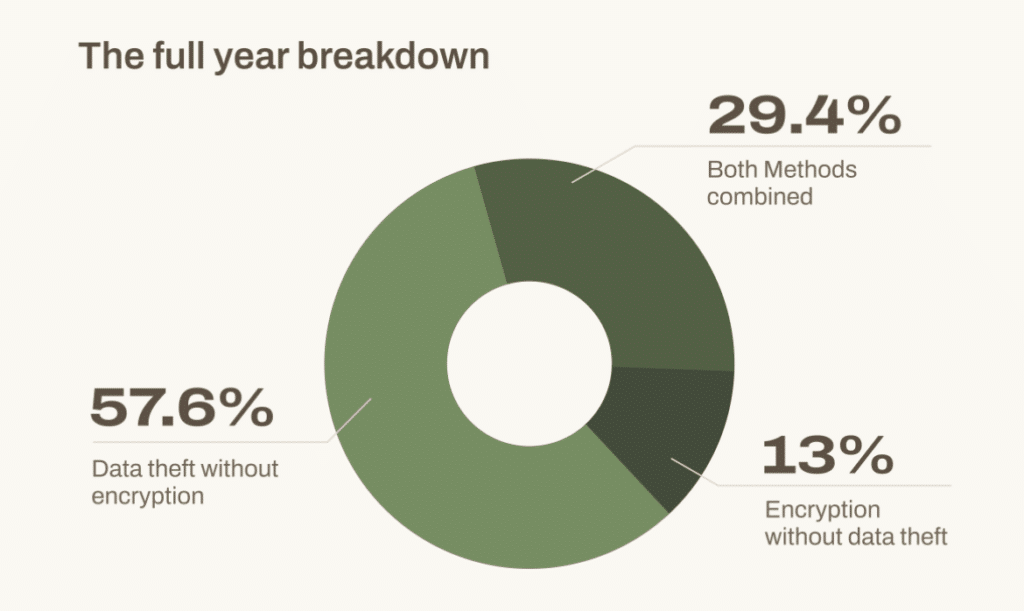
A chart in the report shows the breakdown for the year: data theft without encryption was the most common at 57.6%, followed by attacks with both encryption and theft at 29.4%, and encryption alone at 13%.
Resilience connects this trend to better backups and recovery methods. Attackers now often avoid complex encryption tools. Instead, they steal data and threaten to release it. The report says this approach takes away “recovery-focused” options for victims.
Resilience CEO Vishaal “V8” Hariprasad framed the stakes in the press release. “Claims data gives us the best and most granular insight,” he said. He highlighted “the long-tail aftershocks that follow.”
Claims Severity Follows Regulation, Reputation, And Litigation
The report warns that exposing data can lead to costs that last for years. It points out the legal, regulatory, and reputational effects that follow an incident. This ongoing impact is called the “tail” of a cyber event.
Resilience Chief Underwriting Officer Maria Long described the payment trap. “Paying for data suppression has proven unsuccessful,” she said. She noted lawsuits often follow even after payment.
The report also notes an increase in privacy-related disputes. Notices about wrongful data collection more than doubled from 2024 to 2025. Lawsuits focused on website tracking and data sharing. Many of these claims were covered by self-insured retentions.
Phishing Jumps To The Top Failure Point
Resilience tracked how attackers first got access. In 2025, phishing was the main cause of failure, leading to 50% of losses, up from 22% in 2024.

The report links this increase to social engineering boosted by AI. It references research showing that AI-driven spearphishing had a 54% success rate, while traditional phishing had a 12% success rate in the same study.
Resilience notes that training still makes a financial difference. They estimate that companies with training lowered their potential risk by over $100,000. Better wire controls reduced overall risk by an average of $795,000.
Vendor Risk Stays A Major Loss Driver
Vendor issues were the second biggest cause of losses. Vendor-related failures dropped from 22% in 2024 to 18.8% in 2025. However, Resilience still reports that outages can be very severe.
The report breaks vendor risk into three types: ransomware at a vendor that disrupts clients, vendor breaches that expose client data, and non-malicious outages that still have a real business impact.
Resilience Global Head of Claims Jeremy Gittler offered a blunt summary. “You can outsource your services, but you cannot outsource your risk.”
Identity Becomes The New Perimeter
Resilience researchers see infostealers as an important warning sign. They report that infostealers collected two billion credentials in the first half of 2025 and often showed up before ransomware attacks.
The report urges quick action if there are signs of infostealer activity. It treats credential compromise as an early warning and recommends rotating tokens and assuming a breach if exposure is found.
The press release also stresses the need to act quickly. Resilience ROC leader Judson Dressler describes cyber risk as “an ‘everything, everywhere, all at once’ model.” He says the team looks for stolen credentials and warns clients.
Get The Cyber Insurance News Upload Delivered
Subscribe to our newsletter!
Threat Groups Professionalize Ransom Pricing
Resilience reports that a few groups caused most of the severe losses. A chart ranks ransomware gangs by their share of losses: Chaos led with 35.3%, followed by Interlock at 27.0%.

Resilience points out Interlock’s use of “policy reconnaissance.” The group looks for insurance policies in stolen data. The report says attackers adjust their demands to stay under coverage limits, which puts cyber insurance data at risk.
Scattered Spider also had a big impact in 2025. Resilience connects this group to attacks on retail companies. In one case, the report notes losses of over £40 million per week.
Industry Losses Concentrate In Three Sectors
Resilience reports that manufacturing, healthcare, and retail made up 68% of total losses. Each sector faced its own unique challenges.
Manufacturing had the highest total losses, making up almost 30% of the total. The report links this to just-in-time operations and complex operational technology. Healthcare had the most severe incidents, with costs tied to sensitive records and regulatory requirements. Retail, which had almost no losses in 2024, moved to the highest severity tier in 2025.
Case studies highlight these trends. In one retail case, losses grew quickly because of a vendor outage. In a healthcare claim, almost two-thirds of the budget went to legal costs and reviewing data.
What The Report Urges For 2026 Planning
Resilience expects extortion-only attacks to become more common in 2026. The report predicts more deepfake abuse, quicker identity compromise, and lawsuits following most incidents within days.
The report’s advice is aimed at business leaders. CFOs are encouraged to invest more in prevention controls instead of just backups. CROs should assess tail risk and vendor dependency. CISOs should focus on data loss prevention and stronger authentication against phishing.
For those buying cyber insurance, the main message is to focus on realistic coverage limits. The report recommends choosing coverage that matches the severity seen in 2025, rather than relying on older averages.
FAQ Summary
It analyzes Resilience claims and ROC research from 2025, with 2024 comparisons.
Attackers shifted toward data theft-only extortion instead of encryption.
They rose from 49% of extortion claims in H1 to 65% in H2.
Data theft-only led at 57.6%, with 29.4% using both methods.
Phishing drove 50% of incurred losses, up sharply from 2024.
Infostealers harvested billions of credentials and often appeared before major attacks.
Vendor-related failures remained the second-highest loss category at 18.8%.
The report highlights groups like Chaos and Interlock by incurred loss share.
Manufacturing, healthcare, and retail accounted for 68% of portfolio losses.
It recommends prevention controls, vendor contingency plans, and coverage aligned to 2025 severity.
Related Cyber Liability Insurance Posts
- Trustify Adds Datasurance Cyber Insurance Policy To Trust365 For MSPs
- Ghost Students Exploit Aid as Identity Theft Surges Nationwide – NEW PODCAST
- Fools Rush In – AI Security Lags as Breaches Rise: IBM’s 2025 Data Breach Report
- FAMOUS CHOLLIMA Unmasked: Insights from the 2025 CrowdStrike Report
- Executives Underestimate Cyberattack Costs, Willis Warns in 2025 Report
