Estimated reading time: 1 minute
Most companies think they understand their cyber risk. They filled out the questionnaire. They renewed the policy. The boxes were checked. According to Ralph Pasquariello and Craig Sekowski of CYBERRISKIQ, that confidence is one of the most dangerous blind spots in corporate America today. In the latest episode of the Cyber Insurance News and Information Podcast, the two return as guests to discuss AI’s growing role in cybercrime, their induction into the Society of Risk Management Consultants, and the policy gaps that leave organizations exposed precisely when they think they are protected.
The Number That Changes Everything
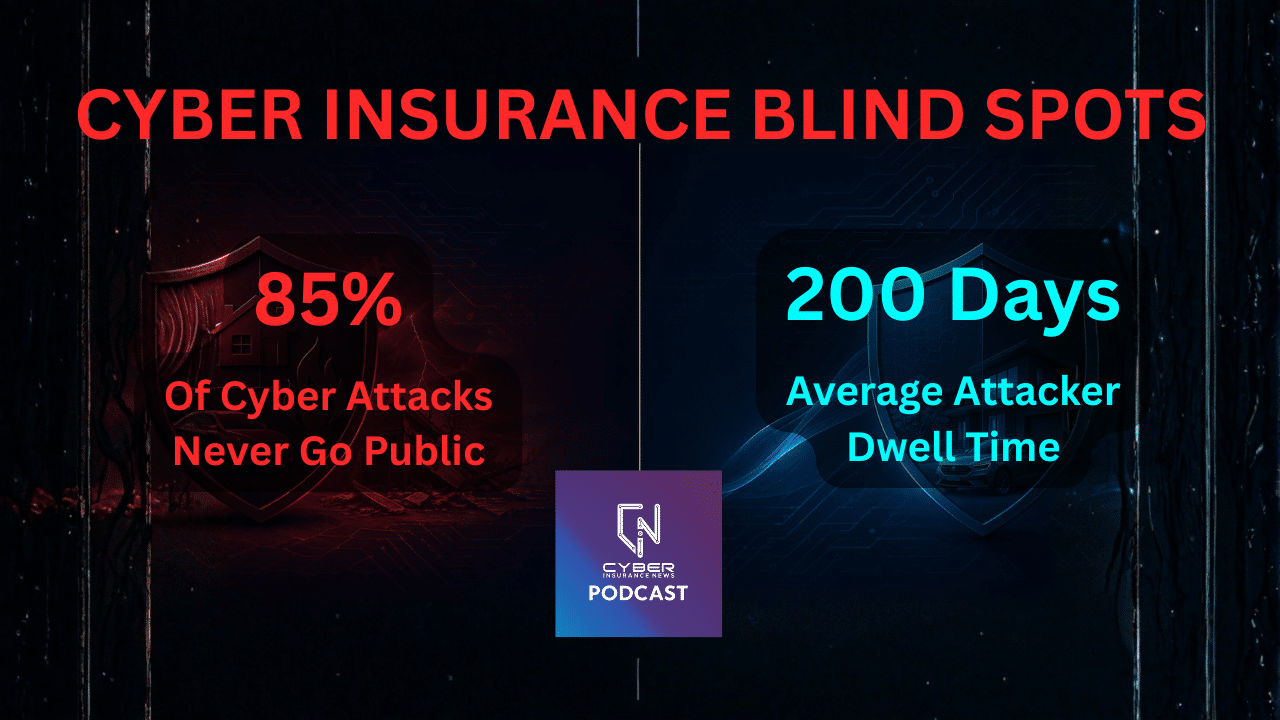
Before discussing coverage, consider the scale of what goes unseen. Pasquariello, drawing on regular briefings with federal law enforcement, states that fewer than 15% of successful cyberattacks ever become public. Breached organizations quietly absorb the other 85% of ransomware payments, data exfiltrations, and business interruptions, often at their own request.
“The first thing the CFO says is I don’t want anyone to know about this,” Pasquariello explains. “And [investigators] have to honor that.”
That silence has a cost. When 85% of the problem stays invisible, boards, executives, and risk managers systematically underestimate the threat. They see a fraction of the incidents, form a fraction of the picture, and make coverage decisions accordingly. The market fills with companies that insure against the cyber risk they think exists rather than the one that actually does.
Watch on YouTube – Other Options Below
ALSO GET THE PODCAST HERE
Spotify
Apple
Amazon
CYBERRISKIQ Joins The Society Of Risk Management Consultants
The news hook for this episode is significant. The Society of Risk Management Consultants vetted CYBERRISKIQ and invited it to join its global body of approximately 158 advisors. The vetting process took three months. The organization does not sell insurance or technology, it advises.
Sekowski frames the significance plainly. Being a known, trusted advisor means operating at a different level than product vendors. “They don’t sell insurance, they don’t sell the technologies, they’re advisors and consultants, and that’s what they do best.”
For the cyber insurance market, this matters. It signals that organizations now treat cyber risk expertise as a core component of enterprise risk management, not an ancillary add-on. When a body of elite global risk consultants formally vets and integrates cyber specialists into their network, the message is clear. Cyber has moved to the main table.
AI Is Changing Both Sides Of The Fight
The episode addresses AI directly and without hype. Sekowski describes it as a tool operating on both sides simultaneously. On the defensive side, AI is identifying vulnerabilities and probing infrastructure before bad actors can exploit them. On the offensive side, criminal networks are catching up fast, using AI to scale attacks, automate reconnaissance, and make phishing indistinguishable from legitimate communication.
Pasquariello flags the insurance implication that most organizations have not yet considered. If the breach was AI-enabled, will your current policy cover it? The answer is not clear. “ddendum Will there be endorsements in the future?” he asks. “There will be addendums coming for AI.”
For underwriters, this is an active underwriting question. For brokers, it is a client conversation that needs to happen now, before renewal, not after a claim.
The Policy Blind Spots Nobody Talks About
The most valuable section of this episode for insurance professionals is the discussion of what Sekowski calls cyber liability blind spots. The pattern Pasquariello and Sekowski encounter repeatedly is a company that has had cyber insurance for years, renewed it automatically, and assumed continuity equals coverage.
One example from the episode: a national packaging company that had renewed its cyber policy for ten consecutive years without a single substantive review. Cybercrime changes every minute. A policy that worked in 2015 fails in 2026. It lacks sufficient limits. It carries outdated exclusions. And it does not address today’s threat landscape.
“For you to neglect even endorsing or making changes on your cyber insurance for ten years, it’s just ludicrous,” Pasquariello states.
The specific gaps they find most often include sublimits on third-party liability that fall far short of actual class action exposure, limits that do not account for notification costs across large record volumes, and AI-related exclusions that nobody flagged at renewal.
Sekowski adds the framing that resonates most with CFOs. “When you have that safety net, which is really your cyber liability, you want to make sure there’s no holes and it’s large enough to catch you.”
Get The Cyber Insurance News Upload Delivered
Subscribe to our newsletter!
What The Market Should Take Away
Pasquariello notes that pricing has flattened, making this an unusually good moment to add coverage layers without doubling premiums. Moving from a $10 million to a $20 million policy does not mean doubling the cost. It means adding layers above the primary. For organizations that have been deferring that conversation, the current market window makes the case straightforward.
The deeper point is structural. Cyber insurance is not a cost center. It is not a checkbox. It is a live document that needs to keep pace with a threat that evolves daily. Companies that Pasquariello and Sekowski engage with understand this. They secure stronger coverage. They prepare more effectively. This positions them to survive the incident they view as inevitable.
The call is already coming from inside the house. The question is whether your coverage is ready when it does.
Podcast Episode FAQ
What is a cyber insurance blind spot?
A cyber insurance blind spot is a gap between what a policy appears to cover and what it actually covers. Common blind spots include sublimits on third party liability, notification cost caps, and exclusions for AI-related incidents that organizations never identified at renewal.
Why do 85% of cyber attacks stay private?
Most organizations that suffer a cyber attack choose not to disclose it publicly. Unless regulatory thresholds are triggered — such as more than 500 records in a HIPAA-covered breach — companies are not required to go public. Federal law enforcement sources confirm that less than 15% of successful attacks ever become known outside the affected organization.
Will cyber insurance cover an AI-enabled attack?
That depends on the policy wording. Many current policies were written before AI-enabled attacks became common. Underwriters are beginning to add AI-related exclusions or endorsements. Organizations should ask their broker directly whether AI-driven business email compromise, deepfake fraud, or AI-assisted ransomware would be covered under their current terms.
How often should a cyber insurance policy be reviewed?
At minimum quarterly, according to Cyber Risk IQ. Annual renewal without substantive review leaves organizations insured for a threat landscape that no longer exists. Cyber crime evolves continuously and policy limits, exclusions, and coverage terms need to keep pace.
What is the Society of Risk Management Consultants?
The Society of Risk Management Consultants is a global body of approximately 158 vetted risk advisors worldwide. Members do not sell insurance or technology — they advise organizations on enterprise risk strategy. Cyber Risk IQ completed a three month vetting process before being invited to join.
What is the average dwell time for a cyber attacker inside a network?
Approximately 200 days. That is the average time between an attacker gaining access to a network and the organization discovering the intrusion. During that window attackers can exfiltrate data, map systems, and prepare for a ransomware deployment without triggering any alerts.
How does a ransom payment become a $10 million problem?
The ransom itself is rarely the largest cost. A ransomware event also triggers a data breach because attackers exfiltrate records before encrypting them. That creates notification obligations, regulatory exposure, class action liability, business interruption costs, and reputational damage — all of which stack on top of the ransom payment itself.
Is cyber insurance pricing rising in 2026?
Pricing has flattened in the current market, making this an unusually good moment to add coverage layers. Moving from a $10 million to a $20 million policy does not mean doubling the premium — it means adding excess layers above the primary, which is generally more cost effective than increasing the primary limit.
Episode transcript.We verified this for accuracy. But check elements against the recording to be sure
Related Cyber Liability Insurance Posts
- The Cyber Insurance Soft Market Is “Finding A Floor” – Will Every Carrier Will Survive?
- Cyber Insurance News & Information Podcast
- What Your Cyber Insurance Policy Misses – And What Attackers Find First – NEW PODCAST
- The Small Business Cyber Insurance And Cyber Security Reality Check – NEW PODCAST
- The Looming Global Cyber Crisis: Are We On The Doorstep of Digital Disaster?