Estimated reading time: 8 minutes
The Numbers Changed. The Rules Changed With Them
The FBI’s 2025 Internet Crime Report delivers one number that sets the stage: losses reported to the Internet Crime Complaint Center reached $20.877 billion last year, a 26% jump from 2024. For insurers, brokers, and corporate risk managers, this confirms the trend. The response to this threat is also clear. The Canadian Cybersecurity Network’s 2026 report, “Cybersecurity Is the New Infrastructure,” details how the market has reacted and what it now expects from any organization that wants to compete.
Insurers Are Setting The New Entry Standard
The CCN report documents the shift with hard numbers. Seventy percent of insurers now require evidence of cyber controls before issuing coverage. Sixty-one percent of organizations report restrictions, delays, or denials in recent applications.
“In a new age of digital trust being a form of critical infrastructure, cyber liability insurance is playing an important role,” said Patrick Bourk, Vice President at Navacord and a contributor to the CCN report. He explains the new reality for underwriting. Insurers are not just pricing cyber risk anymore. They are deciding who counts as a responsible risk. Organizations that lack multi-factor authentication, tested incident response plans, or proven recovery abilities will pay higher premiums, get less coverage, or be left out of the market entirely.
The NetDiligence 2025 Cyber Claims Study backs up this approach. Ransomware and business email compromise are still the main causes of loss. In Canada, the average incident cost about US $874,000. Business interruption losses pushed total claim costs up by over 650%. Now, resilience is what matters most to underwriters. Just focusing on prevention is no longer enough.
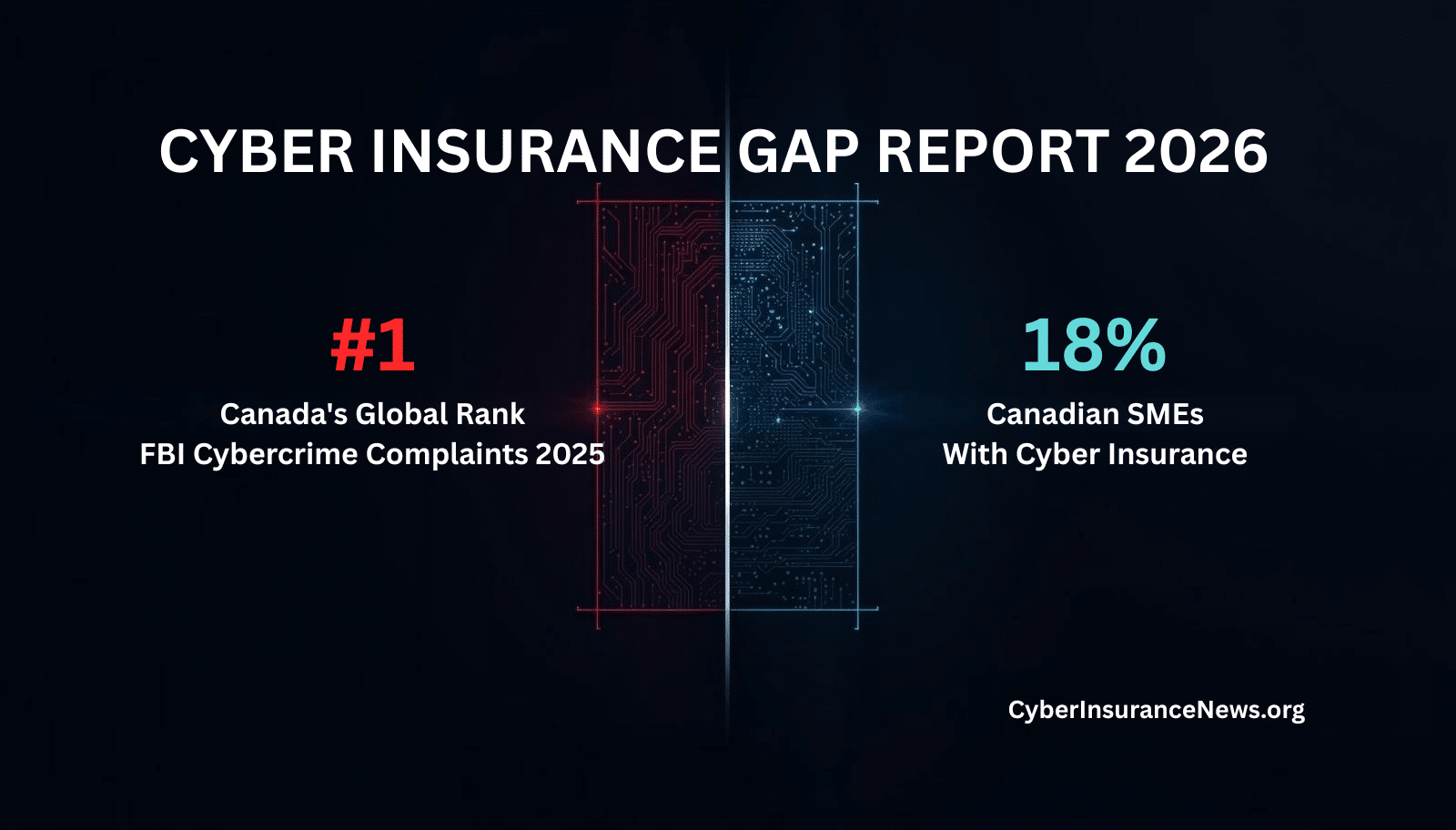
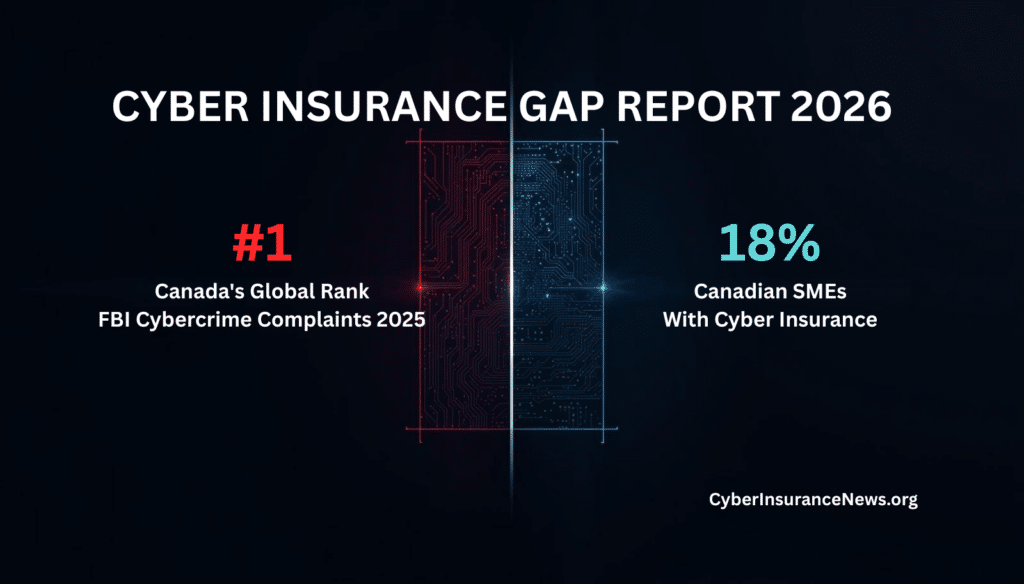
Canada Leads Foreign Complaints. Coverage Lags Far Behind
The FBI’s 2025 data adds one Canada-specific finding worth noting. Canada ranked first among all foreign countries in IC3 complaints, with 7,479 submissions. Canadian organizations appear inside the FBI’s loss universe at a scale that warrants direct attention.
The CCN report adds another concern to this ranking. In 2025, only 18% of Canadian small businesses had cyber insurance. This gap has real business consequences. Supply chains and procurement teams now ask for proof of coverage, and organizations without it are excluded before they can even submit a proposal. François Guay, CEO of the Canadian Cybersecurity Network, puts it simply: “Trust is now the currency that determines who gets to compete.” With only 18% covered, most Canadian small businesses do not have that currency.
Supply Chains Now Enforce Cyber Insurance Requirements
Sixty-three percent of organizations now include cyber insurance status in their vendor risk scoring. Many large institutions require vendors to have $5 million in cyber coverage before any work starts. Procurement teams check a supplier’s cyber readiness before even starting contract talks. If an organization cannot show documented controls, it is removed from consideration before any meeting happens.
Watch Our Podcast
Small Business Cyber Insurance: What Every Owner Needs To Know
Dmitry Raidman, CTO of Cybeats, points out a key problem with relying only on compliance in the CCN report. A SOC 2 Type II certificate or ISO 27001 badge shows a company had controls at one point, but it does not prove the product is secure today. It also does not show that the vendor is always monitoring, communicating, and fixing issues. Now, buyers want to see a Software Bill of Materials, records of vulnerability exchanges, and proof of continuous risk management. Certification alone is no longer enough.
The Trust Question Has Replaced The Security Question
Cyber maturity is now a sign of trust in every business relationship. Insurers see it as a sign of insurability. Procurement teams use it to decide if a partnership is possible. Regulators view it as proof of good governance. Investors are starting to see it as a factor in company value.
The CCN report lists five main forces behind this change: supply chain enforcement, stricter insurance standards, more regulations, digitization of critical infrastructure, and better ways to measure digital trust. Frameworks like CMMC and NIS2 already require verified cyber readiness for market access. Canada’s proposed Bill C-8 shows that local regulations are moving the same way.
Imran Ahmad, senior partner at Norton Rose Fulbright and co-head of Cybersecurity and Data Privacy, states the legal dimension cleanly. “Legal readiness is now a condition of participation in the digital economy.” Organizations without defensible governance and tested incident response find themselves locked out of contracts, insurance, and regulated markets at once.
What Organizations Must Demonstrate Now
The CCN report makes the baseline clear. Multi-factor authentication, tested backup and recovery, endpoint detection and response tools, and a documented incident response plan are now the minimum requirements. These are not ways to stand out, they are simply the basics needed to compete.
Underwriters now look closely at identity security, privileged access controls, third-party risk programs, and real-time verification. The CCN’s State of Cybersecurity in Canada 2026 report found that 91% of users have elevated privileges. The ratio of human to machine identities is now over 1 to 80. These numbers show the risks that underwriters penalize when deciding terms and pricing.
The Gate Is Already Closing
The CCN report gives a clear warning. Organizations are being left out without even knowing it. Coverage is being limited at renewal. Vendors are removed from RFPs before they can submit bids. Partners lose access before any talks start.
Get The Cyber Insurance News Upload Delivered
Subscribe to our newsletter!
FBI data confirms the direction of the threat, and the CCN documents how the market is responding. Today, cyber insurance requirements decide who can take part in commercial markets. Organizations that see these as just compliance tasks may find themselves excluded when it matters most.
Trust is the currency. Proof of cyber maturity is how you spend it.
FAQ: Cyber Insurance Requirements And Market Access
What do insurers require before issuing cyber coverage in 2026?
Insurers now require verified evidence of specific controls before binding coverage. Multi-factor authentication, tested incident response plans, endpoint detection tools, and immutable backup systems are the core baseline. Questionnaires alone no longer satisfy underwriters. They want proof of operational readiness, not stated intentions.
Why are organizations being denied cyber insurance renewal?
Most discover the problem only at renewal. Insurers have tightened underwriting standards in response to rising claims. Organizations that lack MFA, have poor backup integrity, or cannot document tested incident response plans face restricted terms or outright non-renewal. The CCN report found 61% of organizations report application restrictions, delays, or denial.
How do cyber insurance requirements affect vendor contracts?
Procurement teams now screen vendors on cyber posture before engagement. Major institutions require up to $5 million in cyber coverage as a condition of vendor qualification. Organizations without documented controls or current coverage are removed from consideration early in the process, often before a proposal is submitted.
What does cyber maturity mean to an underwriter?
Underwriters assess identity security depth, privileged access controls, third-party risk management, endpoint monitoring, and incident response readiness. The CCN report notes that 91% of users operate with elevated privileges, a direct exposure that underwriters penalize. Cyber maturity is the aggregate signal that determines whether an organization is insurable and at what cost.
How does AI change cyber insurance requirements?
AI-enabled fraud generated $893 million in reported losses in 2025 across more than 22,000 FBI complaints. Underwriters are beginning to price AI-related exposure, including deepfake-enabled BEC and voice cloning scams. Organizations should expect AI governance, model accountability, and synthetic media controls to enter underwriting questionnaires within the next policy cycle.
What is the minimum cyber posture insurers accept?
The floor is moving up. MFA across all systems, encrypted and tested offline backups, an active endpoint detection and response tool, a documented and tested incident response plan, and evidence of patch management discipline represent the current baseline. Below that threshold, organizations face exclusion or prohibitive pricing.
How do ransomware and business interruption losses affect cyber insurance costs?
The NetDiligence 2025 Cyber Claims Study found that business interruption losses inflate total ransomware claim costs by more than 650%. Insurers have responded by scrutinizing recovery capabilities as heavily as prevention controls. An organization that cannot recover quickly is a worse risk than one that gets hit but restores operations fast.
What should Canadian businesses understand about the cyber insurance coverage gap?
Only 18% of Canadian small businesses carried cyber insurance in 2025, according to the Insurance Bureau of Canada. Canada simultaneously ranked first among foreign countries in FBI cybercrime complaints. That combination of high exposure and low coverage creates immediate commercial risk. Supply chains and enterprise procurement programs require proof of coverage. Uninsured vendors are being excluded.
How do supply chains enforce cyber insurance requirements?
Procurement teams now include cyber insurance status and cyber maturity evidence in vendor qualification processes. Suppliers without current coverage, documented controls, or software transparency artifacts are screened out before negotiation begins. The CCN report found 63% of organizations use cyber insurance as part of vendor risk scoring. That number is rising.
What is the legal risk of failing to meet cyber insurance requirements?
Legal exposure operates on two tracks. First, organizations without coverage or documented readiness face greater liability after an incident, as regulators, insurers, and counterparties will scrutinize the gap. Second, organizations that cannot demonstrate defensible governance face contract losses before any incident occurs. Imran Ahmad of Norton Rose Fulbright states that legal readiness is now a condition of participation in the digital economy, not a post-breach consideration.
Related Cyber Liability Insurance Posts
- Marsh Cyber ECHO Hits $200 Million: New Reinstatement Options Close A Critical Coverage Gap
- The Small Business Cyber Insurance And Cyber Security Reality Check – NEW PODCAST
- Protect Your Brand, Not Just Your Data: The Critical Role of ERM in Cyber Risk
- Marks & Spencer Gets $132 million in Cyber Insurance Claims, But Cyber Attack Slashes Profits
- When Cyber Insurance Lets You Down, 831(b) Offers A Plan B – NEW PODCAST